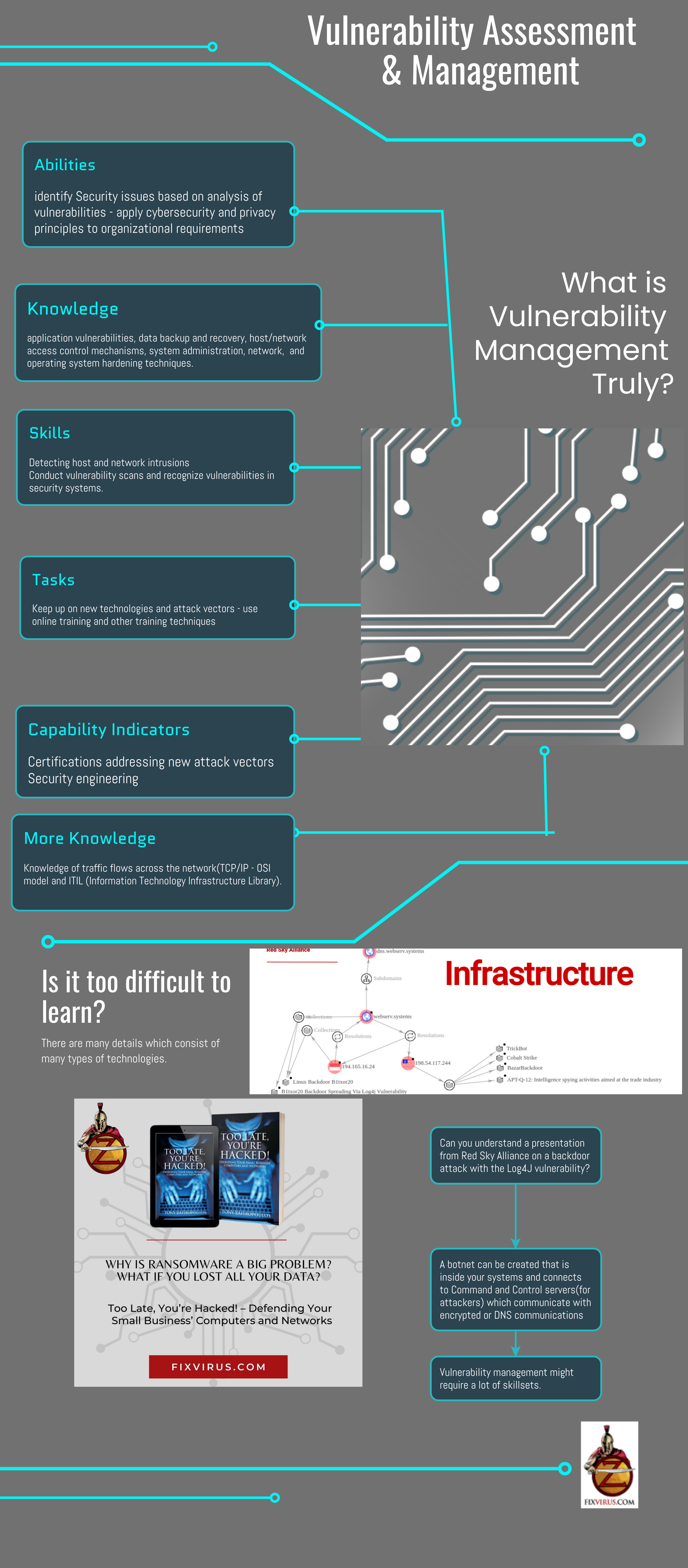
Abilities
Identify Security issues based on analysis of vulnerabilities – apply cybersecurity and privacy principles to organizational requirements
Knowledge
Application vulnerabilities, data backup and recovery, host/network access control mechanisms, system administration, network, and operating system hardening techniques.
Skills
Detecting host and network intrusions
Conduct vulnerability scans and recognize vulnerabilities in security systems.
Tasks
Keep up on new technologies and attack vectors – use online training and other training techniques
Capability Indicators
Certifications addressing new attack vectors Security engineering
More Knowledge
Knowledge of traffic flows across the network(TCP/IP – OSI model and ITIL (Information Technology Infrastructure Library).
Can you understand a presentation from Red Sky Alliance on a backdoor attack with the Log4J vulnerability?
A botnet can be created that is inside your systems and connects to Command and Control servers(for attackers) which communicate with encrypted or DNS communications
Vulnerability management might require a lot of skill sets.
To stay ahead of the game – contact us and buy the book “Too Late You’re Hacked”
CISA.gov webpagehttps://www.cisa.gov/critical-infrastructure-sectors discussing the critical infrastructure sectors that need to be defended
And the skills needed from the National Initiative for Cybersecurity careers and studies (some of the skills needed are included above)
The botnet image is from Red Sky Alliance presentation March 23rd 2022.