Do you have an APC UPS(Uninterruptible Power Supply)?
(Image above from Armis Research)
I do not know which devices actually have these vulnerabilities, assuming Armis research is correct then it may be all devices that connect to the cloud.
Armis Research found some vulnerabilities:
Armis has discovered a set of three critical vulnerabilities in APC Smart-UPS devices that can allow remote attackers to take over Smart-UPS devices and carry out extreme attacks targeting both physical devices and IT assets. Uninterruptible power supply (UPS) devices provide emergency backup power for mission-critical assets and can be found in data centers, industrial facilities, hospitals and more
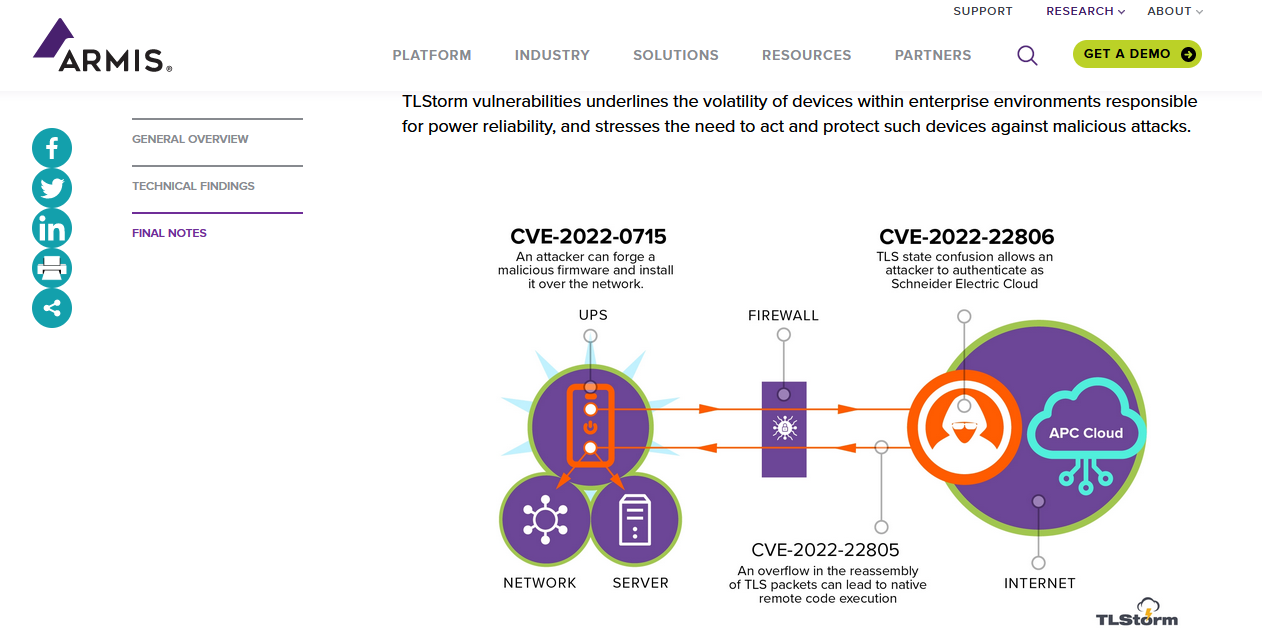
The set of discovered vulnerabilities include two critical vulnerabilities in the TLS implementation used by Cloud-connected Smart-UPS devices, as well as a third critical vulnerability, a design flaw, in which firmware upgrades of all Smart-UPS devices are not properly signed and validated.
Two of the vulnerabilities involve the TLS connection between the UPS and the Schneider Electric cloud. Devices that support the SmartConnect feature automatically establish a TLS connection upon startup or whenever cloud connections are temporarily lost.
- CVE-2022-22806 – TLS authentication bypass: A state confusion in the TLS handshake leads to authentication bypass, leading to remote code execution (RCE) using a network firmware upgrade.
- CVE-2022-22805 – TLS buffer overflow: A memory corruption bug in packet reassembly (RCE).
These vulnerabilities can be triggered via unauthenticated network packets without any user interaction (ZeroClick attack).
The third vulnerability is a design flaw in which the firmware updates on affected devices are not cryptographically signed in a secure manner. This means an attacker could craft malicious firmware and install it using various paths, including the Internet, LAN, or a USB thumb drive. This can allow attackers to establish long-lasting persistence on such UPS devices that can be used as a stronghold within the network from which additional attacks can be carried.
- CVE-2022-0715 – Unsigned firmware upgrade that can be updated over the network (RCE).
You must have a Security policy, and a vulnerability Assessment process. If you are not aware of your devices and what they could have – then it will happen eventually. remember what many security professionals say – it is WHEN you get hacked not IF.
Contact us now.
Buy the book now – Too Late You’re Hacked