What do I mean by “In Time” ? it means that at some point
when a system has old code on it a new attack will have been developed by enterprising hackers both good and bad hackers.
At that point your system is easily hacked, the more time you leave it unpatched the more likely you will get a successful attack.
Of course the devil is in the details. Remember risk management only works properly when you know all of the risks correctly.
Once a system is hackable the risk has increased, but you are still thinking with old data.
Reminder Risk = Likelihood * Impact
I have said before that Risk Management as we know it has failed us¹
The reason is that it is too complicated and too much time has to be spent on evaluating many impacts and likelihoods. For which all that analysis is wasted anyway when the vulnerabilities are changing constantly with new abilities by the hackers.
The hackers do not sit still – #4 on Security News Analyzed³ as of 2/8 is reddit.com/r/netsec and a post in netsec reddit 2 days ago was posted a way to hack a Microsoft SQL Server without a password. Rick Osgood posted his blogpost on Feb 5th at Anitian Blog[4] (a company helping businesses with security issues – one of the good guys) .
In this blog post Rick has found a way to attack the stream of data between a client and Microsoft SQL server (which happened to be a project he was working on -to do a pentest of a Microsoft SQL server.
He was not given a username of the SQL server as this pentest was limited in scope. But what happened was that it seems he uncovered a Man-in-the-Mittle attack on an unpatched server.
StackExchange[5] has a post where they bring up the SQL Server encryption technology upgrade that was made just like in the browser market with SSL3.0 and TLS1.0 being obsolete as far as an encryption standard (which means to be PCI compliant one must upgrade).
Unfortunately there are a lot of SQL server instances running even on client machines so this is a big problem.
This is an interesting snippet from StackExchange:
——————————————————————-
Microsoft has recently revealed (without a lot of fanfare) that they will be investing in TLS 1.2 and phasing out SSL. It should be relevant to all editions of SQL Server.
UPDATE 2016-01-29 : Microsoft has announced official support for TLS 1.2 in 2008, 2008 R2, 2012, & 2014. Downloads and other info can be found in KB #3135244.
——————————————————————-
First thing that happens when you see the list of updated SQL servers, is that any older SQL Servers are not going to be updated.
Here is an image shot from Microsoft Support website[6]
There are 13 SQL Server 2000 versions and 14 SQL Server 2005
The final date of extended support for SQL Server 2005 is 4/12/2016.
Did you know SQL server has to be updated period? All software and hardware goes through this lifecycle issue.
If you are not paying attention to what is in your network and computer systems you will not know these leaky computers. A SQL Server 2005 is susceptible to ingenious programmer hackers. and Rick Osgood is one of the good guys, so the bad guys are doing their own research and they will not conveniently tell us what they are up to until we see the headlines in the news that XY corporation has had it’s database stolen.
In PCI v3.1 compliance at
1.1.6 Documentation and business justification for use of all services,
protocols, and ports allowed, including documentation of security features implemented for those protocols considered to be insecure
1.1.6a Verify that firewall and router configuration standards
include a documented list of all services, protocols and ports,
including business justification for each—for example,
hypertext transfer protocol (HTTP) and Secure Sockets Layer
(SSL), Secure Shell (SSH), and Virtual Private Network(VPN) protocols.
How can one create justification and a list of all ports without a list of software and hardware?
It only stands to reason that a list of software and preferably it’s lifecycle date of End support is important.
When the system has reached End Of Lifecycle it has to be upgraded.
If you are unaware of software on desktops and servers you may have unwittingly opened a door for the hacker to attack you.
This is exactly what I was trying to portray in the Risk Management Model that is Hacked at the lower levels.
As companies’ resources get older and End of Lifecycle (not to mention just patched less frequently). the ingenious hackers go for the easy to hack systems. and once they are on those systems, the Rick Osgoods can hack your computers with Man-in-the-Middle attacks.
So what was a hard to attack computer is now a target when the Moderate and Limited Impact machines are hacked.
The risk management model does not allow for the potential of what if A and B system is hacked and the attacker is on the network.
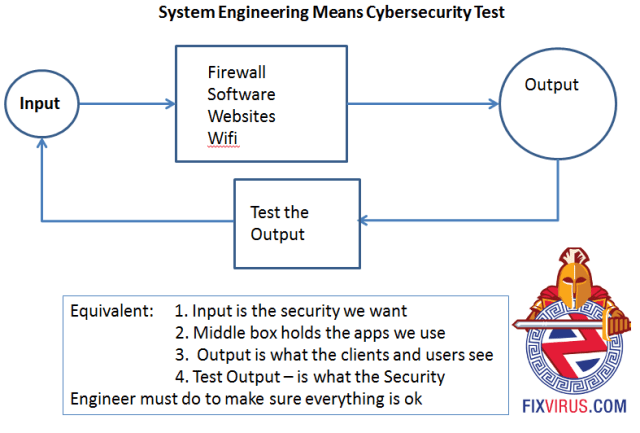
My recommendation is to use a different model
Use System engineering principles: test the systems as they are (no matter their status or otherwise) just like Rick Osgood has done. And then go from there – otherwise not patching in time will Hurt bad as these things have a tendency to catch up with you.
Contact me to discuss
- http://oversitesentry.com/why-risk-management-model-failed-us/
- https://fixvirus.com/ Do you know what you don’t know?
- http://oversitesentry.com/security-news-reviewed/
- https://blog.anitian.com/hacking-microsoft-sql-server-without-a-password/
- http://dba.stackexchange.com/questions/107820/sql-server-compatibility-with-new-tls-standards
- https://support.microsoft.com/en-us/lifecycle?p1=2855





[…] more info in this past post² (Feb 8th, […]