The Microsoft Security Response Center just released the following
Microsoft Mitigates Outlook Elevation of Privilege Vulnerability
Microsoft has developed a script to see if you are already infected by hackers: https://microsoft.github.io/CSS-Exchange/Security/CVE-2023-23397/
The script can run on Exchange server or on Azure based mailboxes(AzureEnvironmentName, AzureADEndpoint, EWSOnlineURL, and EWSOnlineScope can be left as default).
This is a good thing.
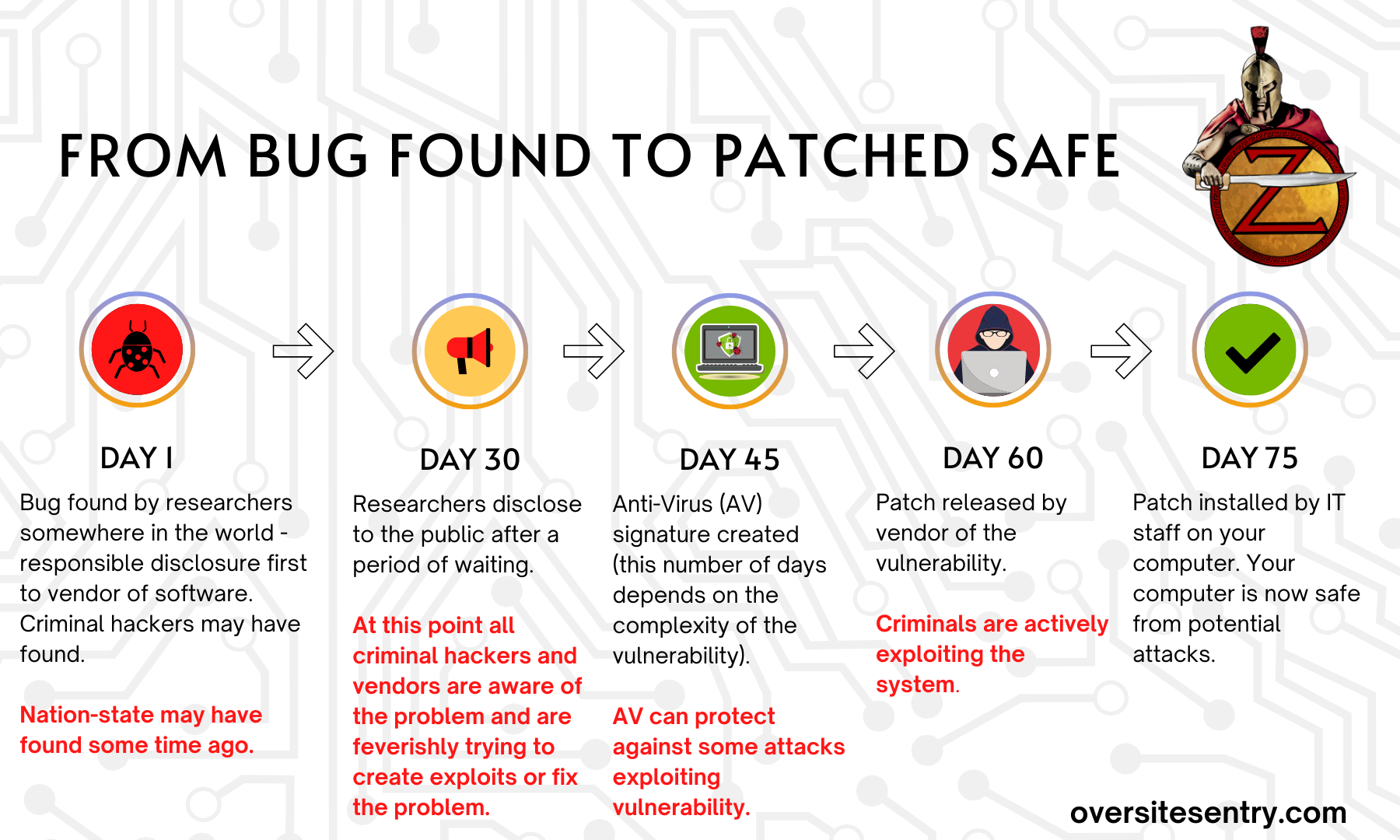
I discuss installing patches as soon as possible due to the leadup of how long it takes to create a patch in the past as well as in my book “Too Late You’re Hacked”
The latest image that I created is called “From Bug found to Patched Safe”
You see the day the Outlook vulnerability was found was months ago while it was released on 3/14 (on Patch Tuesday)
Here is a NIST(National Institute Standards &Technology) bulletin placing this vulnerability at a 9.8 criticality on a scale of 0(lowest)-10(highest).
So this vulnerability (Outlook Elevation of Privilege) was found by researchers or Microsoft at an undisclosed time – as at this point I can’t find it on the usual areas (CVE, Mitre, NIST, and general Internet search). So I must recommend that you should patch(or update) your systems as quick as possible to ensure you will not be taken advantage of an attack coming into your environment.
(Answering the headline question — How important is this patch)
Because if you get hacked the hacker now might get admin privileges, which can be used for more mayhem.
Purchase my book “Too Late You’re Hacked” to get a better understanding of why this is needed (to upgrade) as soon as practical.
Contact me to discuss.