What does this Headline mean to you? From the Talos Intelligence website¹.
The text may be a bit hard to read, so here it is:
Intel HD Graphics Windows Kernel Driver (igdkmd64) Code Execution Vulnerability
Vulnerability: CVE-2016-5647
Summary: A vulnerability exists in the communication functionality of Intel Graphics Kernel Mode Driver. A specially crafted message can cause a vulnerability resulting in executing arbitrary code. An attacker can send specific message to trigger this vulnerability and escalate his privileges on the local system.
But I am asking what does it actually mean? Does it mean to just let the hackers do what they will?
My assertion is exactly that the hackers will have a field day with this vulnerability because it has already been 4 months since vendor notification.
Timeline
2016-03-07 – Vendor Notification
2016-07-11 – Public Disclosure
And now the public(i.e. hackers in Russia/China/etc) know about it.
The game is truly on now – the hackers are trying to figure out a hack and Intel/Microsoft are trying to create a good patch that does not break everything else on the computer.
we have discussed this before²:
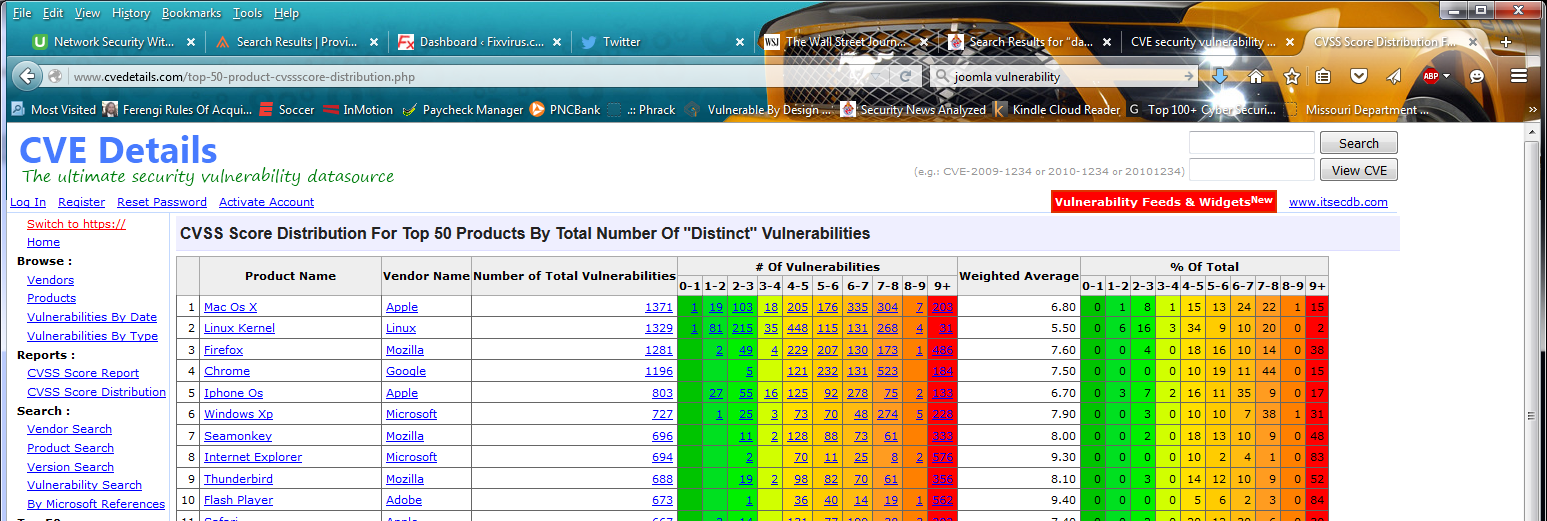
Above is a picture of all the CVE (Common Vulnerability Exploits) with over 10000 CVSS scores of 9-10. The vulnerability that Talos uncovered is 8.4 (as you can see above).
So ho hum there are thousands of “dangerous” CVE’s and another 8.4 CVE is out. So big deal. Most executives do not understand this grand game, and the hackers will always have this ‘upper‘ hand. Remember that the hackers in Russia and China can also do security research to find what exploit can attack our computers. So while Talos is doing their research the Chinese and Russian hackers are also doing their research. This is a constant battle of wits. And realistically the hackers are already in our computers. There are things you an do, but we have to assume they are already in the network.
So yes the blog headline is correct – We may as well say: “Hackers Please Attack Us”
Contact me to discuss
Even after the patch is created in the months to come everyone has to install it and reboot. And preferably they need to test it in their environment first, so the reality is that even after the patch is created there will be thousands of computers that are not patched yet.
I.e. the hackers will have willing targets for their attacks (as soon as they create them) just like they have been doing all along for many months after the fix to the Graphics kernel vulnerability discovered by Talos.
Notice something has happened in the last few years, the prevalence of major viruses³ (like Code Red, Melissa, ILOVEYOU, and more names has been reduced). what has happened is the criminals have taken over from the virus writers. This criminal is more insidious as they are trying to work under everyone’s radar. Now only a few companies that do not have their act in gear with patching and other defenses get ransomware.
And the businesses or individuals that do get them do not talk about them (unlike when the whole world got Melissa).
We are in a different age a much more difficult age and thus you must get more sophisticated – Contact Me at 314-504-3974 or tonyz”@”fixvirus.com
- http://www.talosintelligence.com/reports/TALOS-2016-0087/
- http://oversitesentry.com/zero-day-attacks-and-why-patching-means-catching-up/
- http://oversitesentry.com/assume-you-are-hacked/