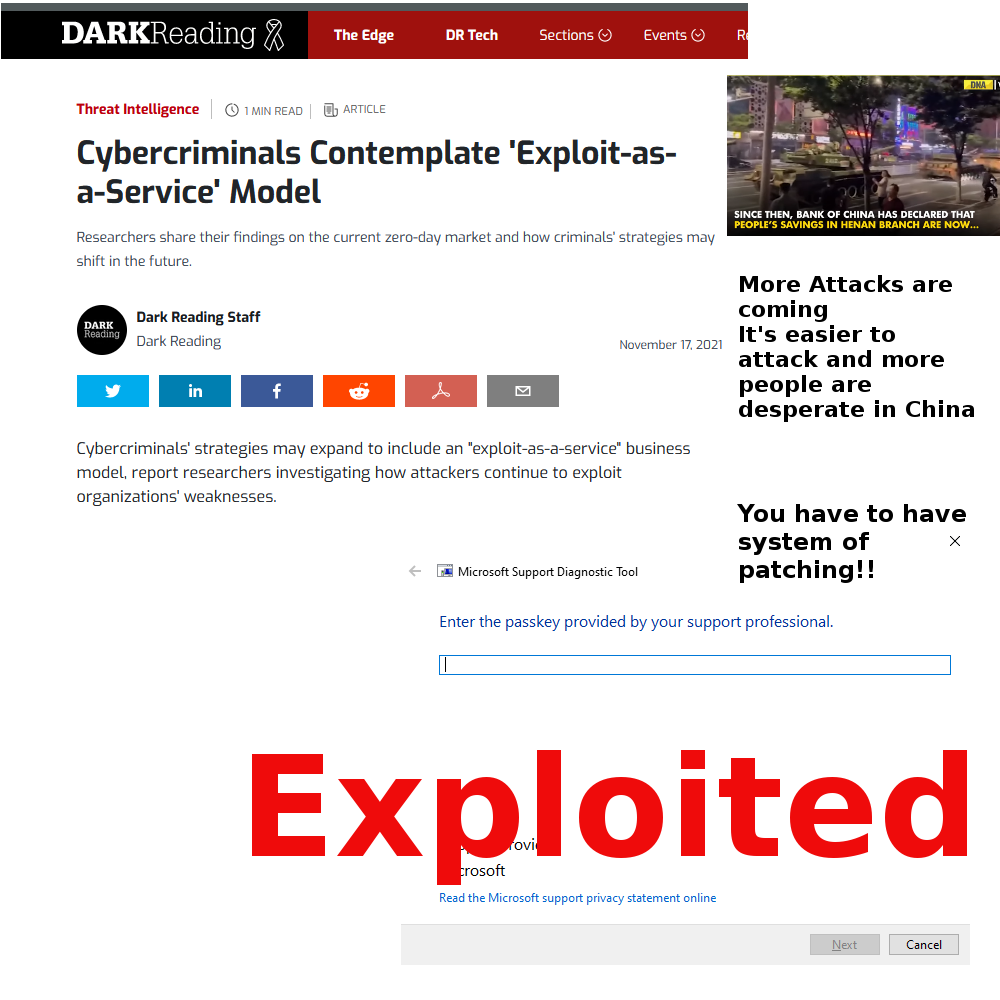
A new Vulnerability which was a “Zero Day” vulnerability in a Windows Tool called MSDT (Microsoft Support Diagnostic Tool) according to Technewsworld.com story
You can see the tool here in the following image: (after typing msdt in the Run or task search bar for Windows`10 operating system.)
As I have discussed before – in many posts the IT departments should keep up on patching so as to keep system safe from as many vulnerabilities as possible.
Hackers have it easier and easier these days as there are “as a service” criminals allowing the hacker to have less and less technical abilities to attack us. Like explained in a Dark reading article:
The Digital Shadows Photon Research Team collected evidence from cybercriminal markets and forums to better understand how vulnerabilities are bought and sold. They report some high-profile criminal groups, such as ransomware gangs, have amassed enough funds to compete with traditional buyers of zero-days — an expensive and competitive market, researchers note.
Their investigation revealed criminals discussing ideas for an exploit-as-a-service model that would “inevitably lower the barrier” for accessing these sophisticated exploits, the team wrote in a blog post.
“This model would allow capable threat actors to ‘lease’ zero-day exploits to other cybercriminals to conduct their attacks,” the report states. The benefit goes both ways: A developer can earn high profits when selling a zero-day exploit; however, it takes a lot of time to finalize a sale. This model would let developers generate even more earnings by renting out their exploits while waiting on a buyer.
In essence one no longer needs to create their own zero-day attack, all one has to do is to rent the ability to run the attack from someone else. One Criminal can focus on making exploits and then sell them online(darknet). The sophistication of the actual attacker are does not have to be high, since the
This is similar to Ransomware as a service (RaaS). Ransomware as a service (RaaS) is a subscription-based model that enables affiliates to use already-developed ransomware tools to execute ransomware attacks. Affiliates earn a percentage of each successful ransom payment. (from upguard website)
There are other patchable vulnerabilities that are important to patch like the Log4Shell problem i discussed earlier this year and late last year. So it seems I am discussing this phenomena again and again – Always the same EOL and patch/upgrade – may as well get used to it and upgrade everything!!!
Notice how in past posts the patch was available (for Log4J/Log4Shell) but yet was not patched by IT departments. Why are we not doing what we have to do? Real life gets in the way – as some servers are hard to reboot(require off hours reboot).
So what happens if you do not patch? Any criminal or out of luck person in a difficult to live area (like China) it could be easier to start a criminal endeavor especially if it is easy to get started.
The longer we do not patch vulnerabilities (Log4J – Dec2021) (MSdt – June2022)
The ransomware as a service model allows underground businesses to flourish especially as things become more chaotic in China. – Patch your stuff the attacks will increase not decrease with time!!
You have to have a system of patching just like mentioned in my book: “Too Late You’re Hacked”