is everything fixed now about 4 months after the vulnerability was disclosed (and discussed here December 13,2021)
So on this day in March (the 4th) Threatpost has a story from a few days ago:
Millions of Java Apps Remain Vulnerable to Log4Shell (a Log4J vulnerability)
The main sentences in the story are the following:
“Researchers did a search on the Shodan search engine to see how many apps vulnerable to Log4Shell are exposed to the internet. They identified 90,000 potential vulnerable internet-facing applications, which they believe “is just the tip of the iceberg in terms of the actual vulnerable attack surface,” Perkal wrote.
Under Active Exploitation
Perhaps most worrying about the vulnerable attack surface is that Log4Shell remains a hot target for threat actors, researchers noted. Indeed, attackers immediately set upon the bug once it was discovered—already under active exploitation—and haven’t let up much since.
While Apache released a patch for Log4Shell within a day of discovery, it, too, had issues that could lead to DoS attacks—and apparently still hasn’t been applied in many cases.”
Also interesting is the following:
“Most recently, active exploitation of Log4Shell has been linked to the Chinese APT 41 group and Deep Panda, Perkal said. Before that, the Chinese state-sponsored espionage group HAFNIUM and Iranian-backed groups APT35 (aka Newscaster) and Tunnel Vision also targeted the flaw.
Currently there are still dozens of recorded daily exploitation attempts of Log4Shell, according to a honeypot set up by the SANS Internet Storm Center, researchers noted.”
It is interesting to note that the 4 months since the public release there are still thousands of systems that have not been patched. Thus since the vulnerability is a RCE or Remote code Execution.
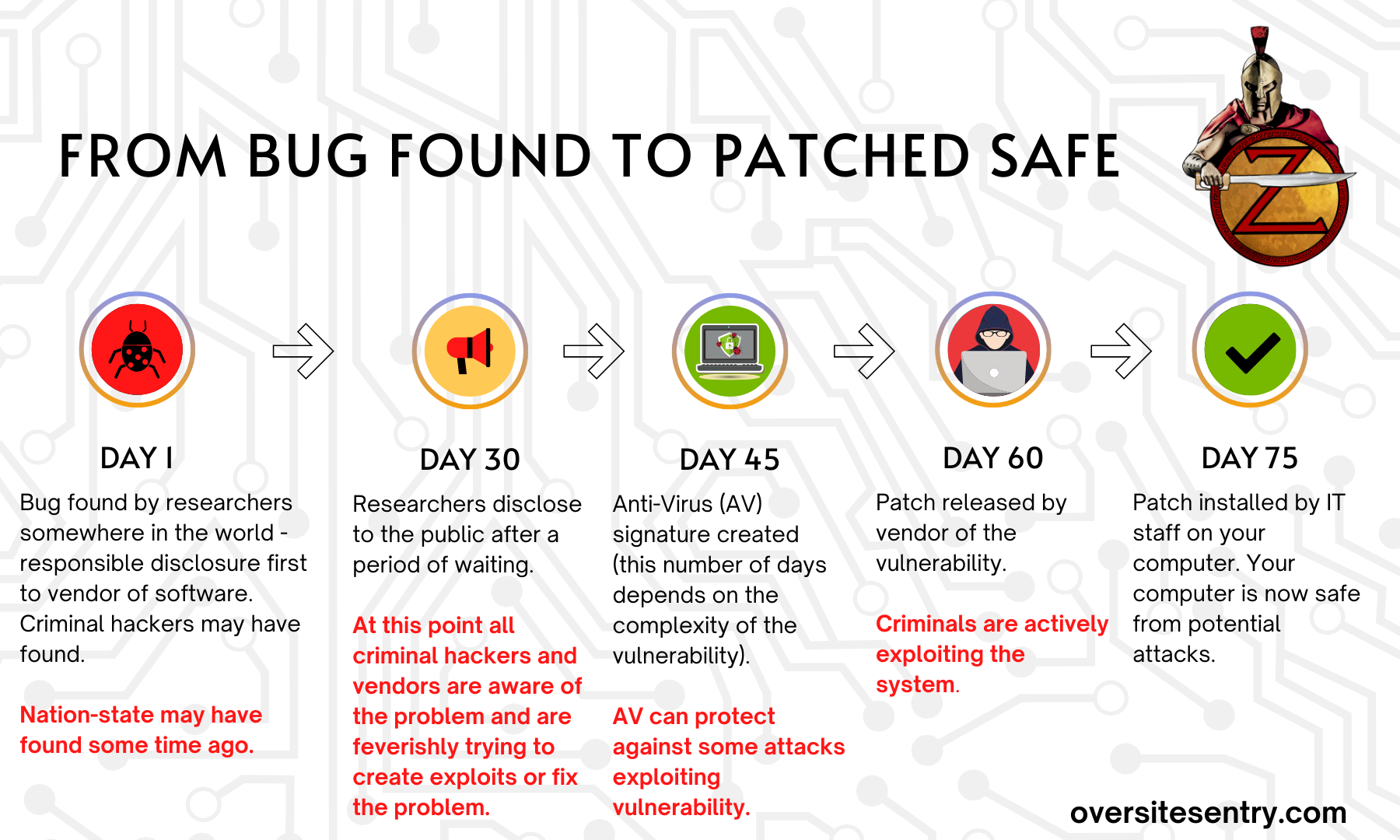
I have put together this handy timeline that reviews where the Log4J vulnerability should be at right now: (at Day 75) where your IT staff should have the systems.
Unfortunately we are now at the point due to many reasons the criminals are taking advantage of IT staffs and environments that are not prepared.
As this story discussed at Arstechnica on 12/14/21 (12 days after release):
“Hackers including Chinese state-backed groups have launched more than 840,000 attacks on companies globally since last Friday, according to researchers, through a previously unnoticed vulnerability in a widely used piece of open-source software called Log4J.”
If there were 840,000 attacks in December – how many were there more than 4 months later?
The criminals are actively looking for weaknesses, and Log4J is a weakness.
So what is happening that we are not performing the patches and other defensive improvements to protect the environment?
Here is an example of an attack that I posted about before (Vulnerability management Just Do IT)
Again this is from a few months ago(March 24th).
What will it take for people in charge to spend more resources to the point where all of the systems are tested and patched?
I think there is an inherent problem with some people that think it is not necessary or another reason with the end result that the systems are not patched.
More info on my book at Fixvirus.com/order-book 12/14/21