We are always being attacked by criminal elements in nation-states that are against us (China – Russia – Iran – and North Korea or NORK). The following information is presented copied from the FBI website https://www.fbi.gov/investigate/cyber/most-wanted
in case you can’t read the small letters here they are starting with the Russian
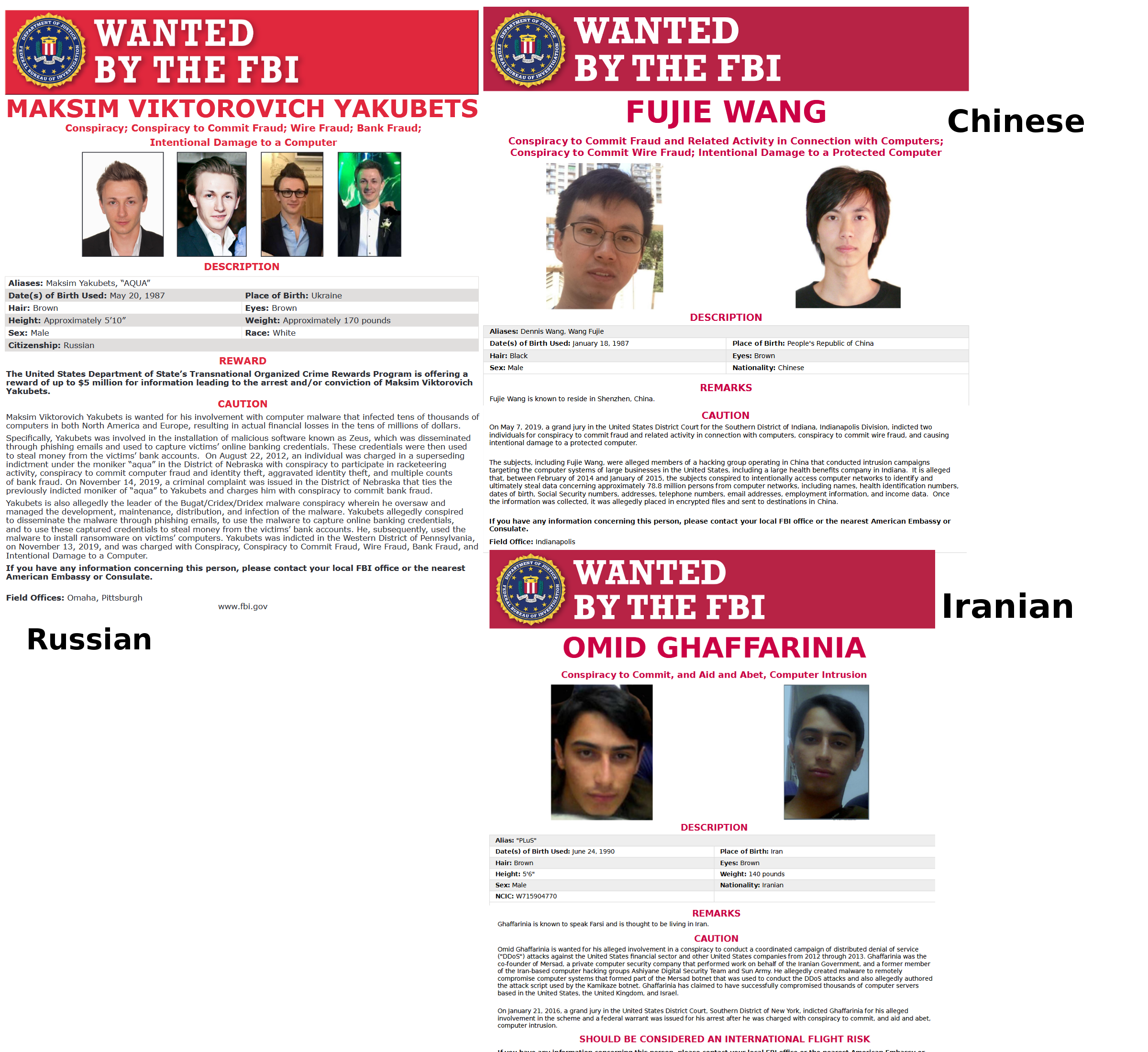
WANTED BY THE FBI:
MAKSIM VIKTOROVICH YAKUBETS
Conspiracy; Conspiracy to Commit Fraud; Wire Fraud; Bank Fraud;
Intentional Damage to a Computer
REWARD
The United States Department of State’s Transnational Organized Crime Rewards Program is offering a reward of up to $5 million for information leading to the arrest and/or conviction of Maksim Viktorovich Yakubets.
CAUTION
Maksim Viktorovich Yakubets is wanted for his involvement with computer malware that infected tens of thousands of computers in both North America and Europe, resulting in actual financial losses in the tens of millions of dollars.
Specifically, Yakubets was involved in the installation of malicious software known as Zeus, which was disseminated through phishing emails and used to capture victims’ online banking credentials. These credentials were then used to steal money from the victims’ bank accounts. On August 22, 2012, an individual was charged in a superseding indictment under the moniker “aqua” in the District of Nebraska with conspiracy to participate in racketeering
activity, conspiracy to commit computer fraud and identity theft, aggravated identity theft, and multiple counts of bank fraud. On November 14, 2019, a criminal complaint was issued in the District of Nebraska that ties the
previously indicted moniker of “aqua” to Yakubets and charges him with conspiracy to commit bank fraud.
Yakubets is also allegedly the leader of the Bugat/Cridex/Dridex malware conspiracy wherein he oversaw and managed the development, maintenance, distribution, and infection of the malware. Yakubets allegedly conspired to disseminate the malware through phishing emails, to use the malware to capture online banking credentials, and to use these captured credentials to steal money from the victims’ bank accounts. He, subsequently, used the malware to install ransomware on victims’ computers. Yakubets was indicted in the Western District of Pennsylvania,
on November 13, 2019, and was charged with Conspiracy, Conspiracy to Commit Fraud, Wire Fraud, Bank Fraud, and Intentional Damage to a Computer. If you have any information concerning this person, please contact your local FBI office or the nearest American Embassy or Consulate.
Field Offices: Omaha, Pittsburgh
Next is Chinese:
FUJIE WANG
Conspiracy to Commit Fraud and Related Activity in Connection with Computers; Conspiracy to Commit Wire Fraud; Intentional Damage to a Protected Computer
REMARKS
Fujie Wang is known to reside in Shenzhen, China.
CAUTION
On May 7, 2019, a grand jury in the United States District Court for the Southern District of Indiana, Indianapolis Division, indicted two individuals for conspiracy to commit fraud and related activity in connection with computers, conspiracy to commit wire fraud, and causing
intentional damage to a protected computer.
The subjects, including Fujie Wang, were alleged members of a hacking group operating in China that conducted intrusion campaigns
targeting the computer systems of large businesses in the United States, including a large health benefits company in Indiana. It is alleged
that, between February of 2014 and January of 2015, the subjects conspired to intentionally access computer networks to identify and ultimately steal data concerning approximately 78.8 million persons from computer networks, including names, health identification numbers, dates of birth, Social Security numbers, addresses, telephone numbers, email addresses, employment information, and income data. Once the information was collected, it was allegedly placed in encrypted files and sent to destinations in China. If you have any information concerning this person, please contact your local FBI office nearest American Embassy or Consulate.
Now for the Iranian:
OMID GHAFFARINIA
Conspiracy to Commit, and Aid and Abet, Computer Intrusion
REMARKS
Ghaffarinia is known to speak Farsi and is thought to be living in Iran.
CAUTION
Omid Ghaffarinia is wanted for his alleged involvement in a conspiracy to conduct a coordinated campaign of distributed denial of service
(“DDoS”) attacks against the United States financial sector and other United States companies from 2012 through 2013. Ghaffarinia was the co-founder of Mersad, a private computer security company that performed work on behalf of the Iranian Government, and a former member of the Iran-based computer hacking groups Ashiyane Digital Security Team and Sun Army. He allegedly created malware to remotely compromise computer systems that formed part of the Mersad botnet that was used to conduct the DDoS attacks and also allegedly authored the attack script used by the Kamikaze botnet. Ghaffarinia has claimed to have successfully compromised thousands of computer servers based in the United States, the United Kingdom, and Israel. On January 21, 2016, a grand jury in the United States District Court, Southern District of New York, indicted Ghaffarinia for his alleged
involvement in the scheme and a federal warrant was issued for his arrest after he was charged with conspiracy to commit, and aid and abet,
computer intrusion.
SHOULD BE CONSIDERED AN INTERNATIONAL FLIGHT RISK
If you have any information concerning this person, please contact your local FBI office or the nearest American Embassy or
Consulate.
Field Office: New York
Notice that all three people from 3 different places around the world are creating malware attacking us by managing or directing attacks. This is happening all the time with many different people these 3 are just the tip of the iceberg.
Here is my attempt at explaining what is happening to us with Cyberhumor:
Russian, Chinese & Iranian hacker walk in bar. Russian says you hacked bar yet? Who pay Vodka?
The Chinese says not yet, but I think I pay with Iranian friend wallet.
The Iranian said yes hacked yesterday and stole all credit card # and put in my wallet.
Contact me for information on how to prevent hackers getting into your environment.