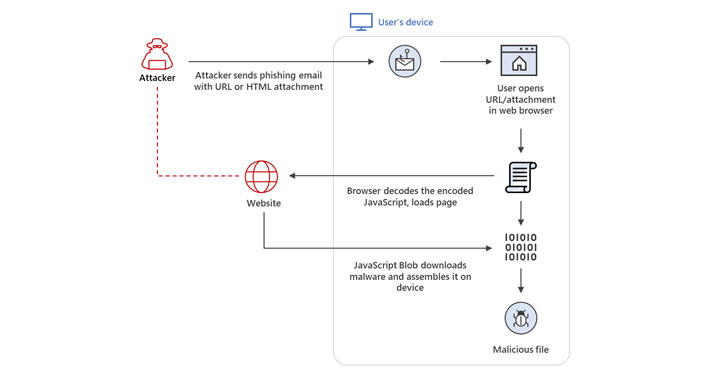
Hacker News has an article on how Hackers use a method of installing their
software onto your systems.
1. If you notice the problem is when the user opens an attachment or link (URL) in their web browser(Firefox – Microsoft Edge, or Google chrome among the most used browsers)
2. Then the browser decodes the javacode (which is unintelligible by most people) this leads to a Website (criminal owns this website)
3. The Criminal website now downloads a malicious software (Malware) onto your machine.
4. Here it depends on what the objective of the criminal hacker is – make money? destroy data?
As HackerNews notes here:
Microsoft 365 Defender Threat Intelligence Team, in a new report published Thursday, disclosed that it identified infiltrations distributing the Mekotio banking Trojan, backdoors such as AsyncRAT and NjRAT, and the infamous TrickBot malware. The multi-staged attacks — dubbed ISOMorph — were also publicly documented by Menlo Security in July 2021.
various malware was installed at different times in the past.
there is also software that can steak credentials and send that info back to the command server run by the criminal hackers. this way when you are entering your banking information that info eill be stolen and can be used against you.
So the bottom line is?
Do what you can to defend your computers so they do not receive the initial malware, because once it is on your system and running if your system has a vulnerability then it is over.
So patch/update your systems, run anti-virus, and browser helper programs against ads as well as privacy to cover as many bases as possible.
Get my book “Too Late You’re Hacked” to start working on a systemic method of defense!