I’m often thinking where the next attack can come in and unfortunately it may come where we least expect it.
Spiceworks blogpost has an interesting angle:
How often have cloud services been installed by users without IT department knowledge?
The survey by Spiceworks has found that many IT people have found their users installing cloud services 78% of the time from 2 times to over 5 times.
The Cloud applications that IT people are worried about:
- Cloud Storage (Dropbox, Google Drive, OneDrive) – 35%
- Webmail (Gmail,Microsoft Exchange Online, Yahoo) – 27%
- Messaging Services (Google hangouts, Slack, Yammer) – 9%
- Finance/Accounting applications (Quickbooks Online, FreshBooks) – 8%
- Productivity Tools(Office Online, Google Docs) – 4%
- CRM& SFA (Salesforce, Zoho CRM) – 3%
- Other – 4%
I would think games are also a big portion. Bigger than 4% inside of others.
As you read down the list of cloud applications, some are easier to access than others. Gmail, Google hangouts and Google Docs are accessed with a login on a browser. I think that Google applications are not inherently unsafe it is only when a document is downloaded within Gmail or Google Drive is when the danger goes up. Although many online cloud apps do not require plugins or other software to be downloaded, many do so that is one way of infection (downloaded plugins).
Accessing personal email in the company network with Yahoo, online Exchange, Gmail or any other email service is not just a “breach of protocol”. The user may unknowingly add streams of spam and phishing emails which will try to take over the machine of the user.
So let’s say you invested into a program or service which checks company emails for viruses and other malware, obviously the personal emails accessed will not be using your ‘safety’ program. Now all of a sudden more viruses and malware are installed (in a hidden manner).
The same goes for messaging services. I think it is hard to see that online accounting programs could have malware, the chance may be less, but it could happen where files are downloaded which have malware in their files.
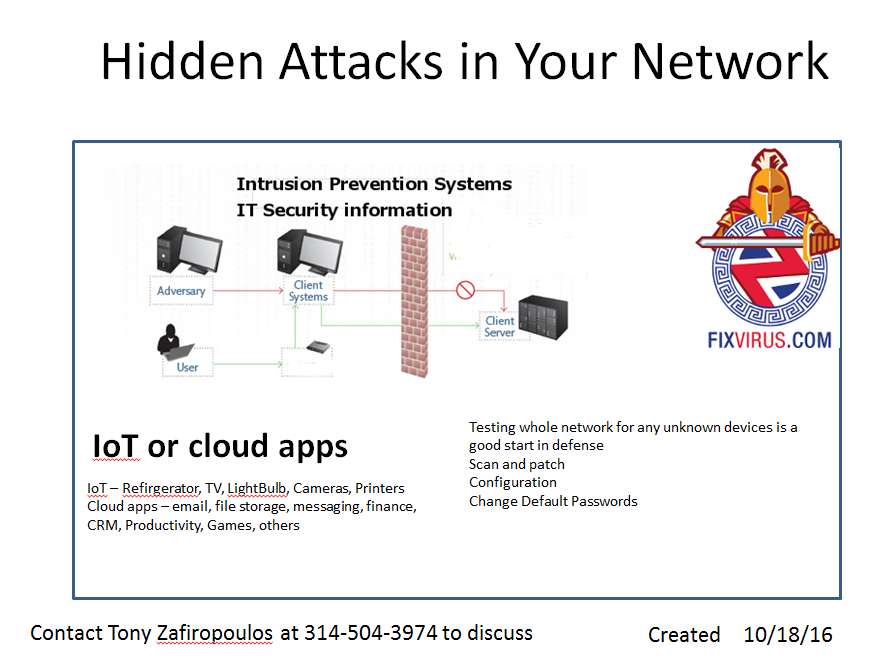
This is the reason an IPS(Intrusion Prevention System) is needed.
It is very hard to accurately predict all user actions so another layer of defense at the Firewall/network would be a good thing.
We know how to do our jobs of defending the network and perimeter, and the hacker finds any nook and cranny to get through this defense.
On the network we have TTP: Tactics Techniques and Procedures. Technology (firewall and endpoint protection), and the procedures are where people are using their personal email in a company computer.
More attacks come on where hackers can get in that is least defended. Like your unknown network devices:
And then if a system (like an IoT – Internet of Things) i.e a new refrigerator, TV, Lightbulb, and really any other device (like a camera attacking using DDOS in this post) that is on the network can be hacked.
The hacker has tools like ncat and other innocuous programs that can be used by an enterprising person.
IPS systems properly configured can at least provide some defense to these odd attacks. But there is no foolproof defense – just constant surveillance and review as well as patching, configuration updates as needed.
Not to mention that GRC(Governance, Risk , Compliance) is also important to keep track of all programs and devices on your network. GRC provides context and priority for attention.
Contact Us to discuss



[…] Hidden Hacks In Network […]
[…] have discussed this IoT powder keg before in our “Hidden hacks in Network” Also “IoT Botnet can DDOS Your […]