Let’s set this up…
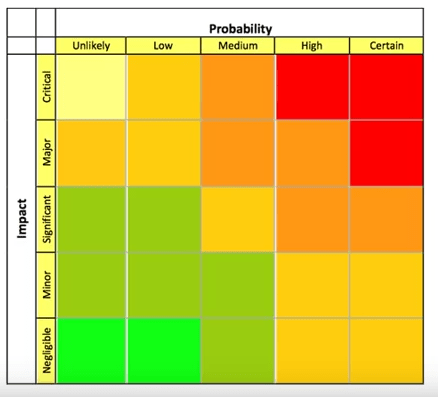
You have paid attention to some Cyber security efforts, and have a number of defenses, maybe not “all of them” but your risk management matrix has shown you where to focus. What is impact on a device if having Cyber security problems?
Assuming you set up the probability matrix of all of your devices failure impact… Did you think of everything?
What about this:
Internet Storm center has a story “More malspam pushing Lokibot”
The post is about when an email attachment RTF(Rich Text Format) runs and then downloads an exploit for CVE-2017-11882 which installs Loki the information stealer.
Once Loki is on the machine it will contact home base and more.
Loki is an especially bad malware software, as it steals FTP credentials, SMTP credentials, Browser data, database information, and keylogger abilities.
So how do we defend against this malware? we need to deny the entry points. Because if once the malware is in one of your systems or one of your partners then it is a different game.
So what happens when you think the neighbor is infected? The firewall is no longer in play, as all internal machines are now open to attack. All it takes is another payload to be dropped into the infected machine that will take advantage of other machines with weak defenses.
So the problem is that any machine that you allow into your network (with vpn or otherwise) also can make your network systems weaker.
Coming back to our neighbor, if the neighbor does not have the same methods to security as you do, they are now a liability if you do not take the neighbor threat seriously.
I want to give an example in an apartment building that has been setup with a well known ISP internet service. So you get an apartment and the service for internet is built-in to the price of your apartment(or at least is a minor add-on).
The Apartment people tell you to just plug into the wall and voila you have internet service.
So when i plug in, do i get my own router? Or am I connected within a switch with every other apartment first? So now I have to run a discovery scan, and check all other IP addresses first?
This is why one runs a discovery scan, to see all the machines that are on the network and that can see you. This is all part of the risk management of your company.
Contact Us to discuss Risk management and more.