The Exchange server hack keeps on going:
https://www.technewsworld.com/story/87095.html : (April 13 story) Fortune 500s Hit by MS Exchange Breach Maybe still unaware.
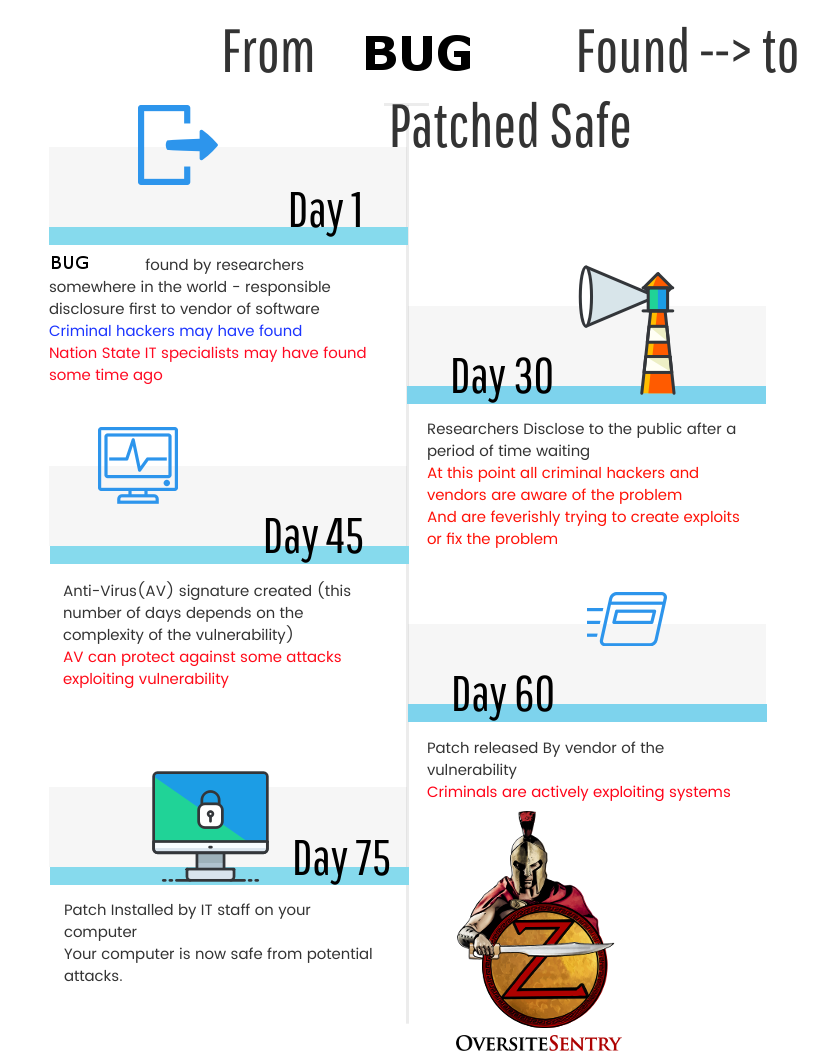
Although this article lists a lot of Fortune 500 companies with large budgets, they seem to have missed the Microsoft Exchange Server vulnerability fix. Probably the reason is that this specific problem was close to a Zero Day
“The Microsoft Exchange breach focused on stealing email from some 30,000 organizations by exploiting four newly-discovered flaws in Microsoft Exchange Server email software. That attack seeded hundreds of thousands of victim organizations worldwide with tools that give the attackers total remote control over affected systems, according to published reports.
Intrigue’s network monitoring discovered 120 exposures among the Fortune 500 companies. A total of 62 individual organizations were affected, and 23 organizations had multiple independent systems exposed. One professional services firm was found to have upwards of 25 independent systems exposed, noted Cran.”
were you wondering what industries were hit?
Advertising and Marketing
Apparel
Automotive Retailing, Services
Chemicals
Commercial Banks
Computer Software
Consumer Credit Card and Related Services
Delivery
Diversified Financials
Diversified Outsourcing Services
Electronics
Energy
Engineering, Construction
Financial Data Services
Food Consumer Products
Food Production
General Merchandisers
Home Equipment, Furnishings
Homebuilders
Hotels, Casinos, Resorts
Insurance: Life and Health
Insurance: Property and Casualty (Stock)
Logistics
Medical Products and Equipment
Mining, Crude-Oil Production
Motor Vehicle Parts
Packaging, Containers
Petroleum Refining
Pharmaceuticals
Pipelines
Retail
Securities
Soaps and Cosmetics
Telecommunications
Utilities: Gas and Electric
Wholesalers: Diversified
Wholesalers: Food and Grocery
Wholesalers: Health Care
I’m sure there have to be more industries if one subdivides or separates the economy in a different manner.
But you can see that there is a good cross-section of the economy listed above.
Why am I rehashing this? Because this is a classic IT Cyber issue.
I discuss and talk about this phenomenon in my book.
This exchange server attack has now been attributed to China.
In this Story on Krebs On Security. The earliest report of a problem was in January 5 (DEVCORE was credited with 2 of the 4 patches on March 2).
But if you keep reading the initial attacks were first identified in Europe on January 3rd.
It takes a while before Microsoft actually agrees it is a problem (Feb 2nd)
At that point of the attack this was considered a “Zero-Day” vulnerability since there was no defense and Microsoft was being notified of the problem.
By March 3rd – a release claimed 10s of thousands of Exchange server software compromised. In Fact March 5th Krebs on Security noted 30,000
Here is a blog entry on Microsoft Blog:
“Microsoft has detected multiple 0-day exploits being used to attack on-premises versions of Microsoft Exchange Server in limited and targeted attacks. In the attacks observed, the threat actor used these vulnerabilities to access on-premises Exchange servers which enabled access to email accounts, and allowed installation of additional malware to facilitate long-term access to victim environments. Microsoft Threat Intelligence Center (MSTIC) attributes this campaign with high confidence to HAFNIUM, a group assessed to be state-sponsored and operating out of China, based on observed victimology, tactics and procedures.”
So China was attacking for months without any possibility of a patch (“January 5 and earlier” until March 9th) March 9th is the date of the 2nd Tuesday of the month(Patch Tuesday).
And realistically this vulnerability and breach was likely there for months earlier.
The Chinese had plenty of time to scope out “all” the exchange servers and take them over one by one.
Do you want to learn more about this?
My book(pre-order here) discussed this just like I have done here on this Blog:
Contact Us to discuss