Not just Uber but anyone with a cloud account has an admin account which is susceptible to social engineering hacks. (portswigger article link below)
Google example:
https://support.google.com/a/answer/57919?hl=en
This article is for Google Workspace administrators who manage Gmail accounts for a company, school, or other group. To manage your personal Gmail account, go to the Gmail Help Center.
As an administrator, you can control Gmail access for the users in your Google Workspace organization. You can turn Gmail on for everyone. Or, turn it on for certain groups or departments.
This is the article about Uber that made me think about cloud admin account portswigger Sep16 article
According to the attacker, the hack was set up by spamming an Uber employee with push authentication requests for more than an hour before using another channel to trick them into authorizing one of the requests.
The attacker claims they went on to locate a network share containing powershell scripts that included the username and password of a system administrator.
One has to find out a possible weak link in the organization and sometimes it is the person who administers the cloud.
Look at this older headline: Microsoft warns of a wide -scale phishing-as-a-service
So last year Microsoft found the details of a large-scale Phishing-as-a-Service(PhaaS) operation. They sell phishing kits and email templates “BulletProofLink”
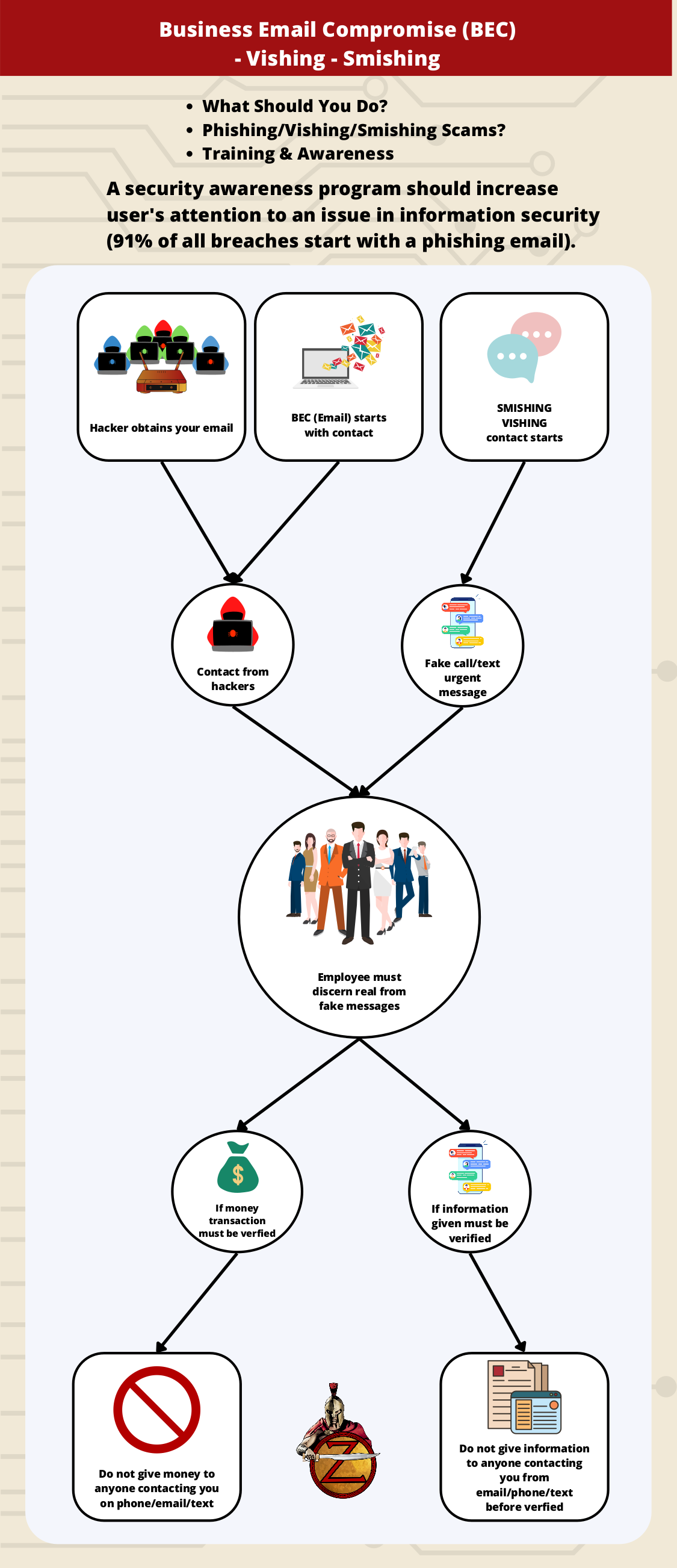
One can see in the image above there is a sustained effort by the criminals to make this attack as simple as possible (where one may not even know too much of the technical details to make an attack). The PhaaS creators intend to sell these kits and the service in general to non-techies, which will only make life more difficult for all of us defending the network.
It is high time to pay attention to your network and systems, audit the network and systems, create a security awareness program asap.
A little more info on the Uber hack:
Bleeping Computer article MFA Fatigue: Hackers’ new favorite tactic in high-profile breaches
The criminal hacker kept trying to log in to a MFA defended account, which caused the account to constantly send out prompts which ask “is this login attempt good?”
MFA is used to counter the possibility of social engineering attacks which gives defense an additional layer of defense. But the hacker attacker is countering this again by using “MFA Fatigue” which just means the criminal hacker will just keep trying until they get the access.
However, a social engineering technique called ‘MFA Fatigue’, aka ‘MFA push spam’, is growing more popular with threat actors as it does not require malware or phishing infrastructure and has proven to be successful in attacks. (from article)
An MFA Fatigue attack is when a threat actor runs a script that attempts to log in with stolen credentials over and over, causing what feels like an endless stream of MFA push requests to be sent to the account’s owner’s mobile device.
The goal is to keep this up, day and night, to break down the target’s cybersecurity posture and inflict a sense of “fatigue” regarding these MFA prompts.
Ultimately, the targets get so overwhelmed that they accidentally click on the ‘Approve’ button or simply accept the MFA request to stop the deluge of notifications they were receiving on their phone.
This type of social engineer technique has proven to be very successful by the Lapsus$ and Yanluowang threat actors when breaching large and well-known organizations, such as Microsoft, Cisco, and now Uber.
Again one must prepare for this possibility – get ready for the attacks.
What should be done to counter the MFA Fatigue attack is to create number matching for Microsoft and “Verified Push” in Duo which is a feature that displays a series of numbers to a user attempting to log in with their credentials.
Contact us for more info.