I bumped intothis site (Dresec)
latest post is “Phishing with Google calendar”
His first sentence is a disclaimer as he does not want other people to use the information to send phishing calendar invites. To him (and me) it is only designed to be a test within our organizations.
Here is the sample calendar invite:
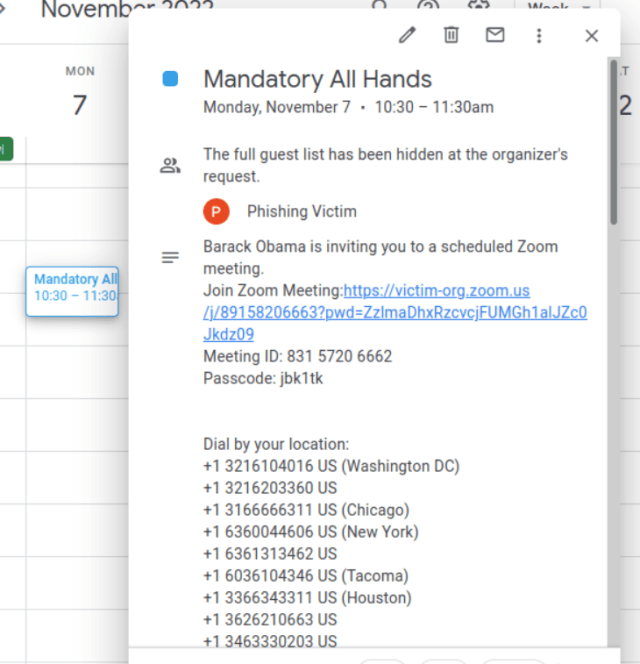 calendar invite in google’s calendar app and the rest of it would insert a link into a fake zoom meeting (obviously one does not need an actual zoom account) as most of the numbers can be faked.
calendar invite in google’s calendar app and the rest of it would insert a link into a fake zoom meeting (obviously one does not need an actual zoom account) as most of the numbers can be faked.
What has to be done is the wording of the meeting and a few other items have to look good (good enough to pass a cursory glance).
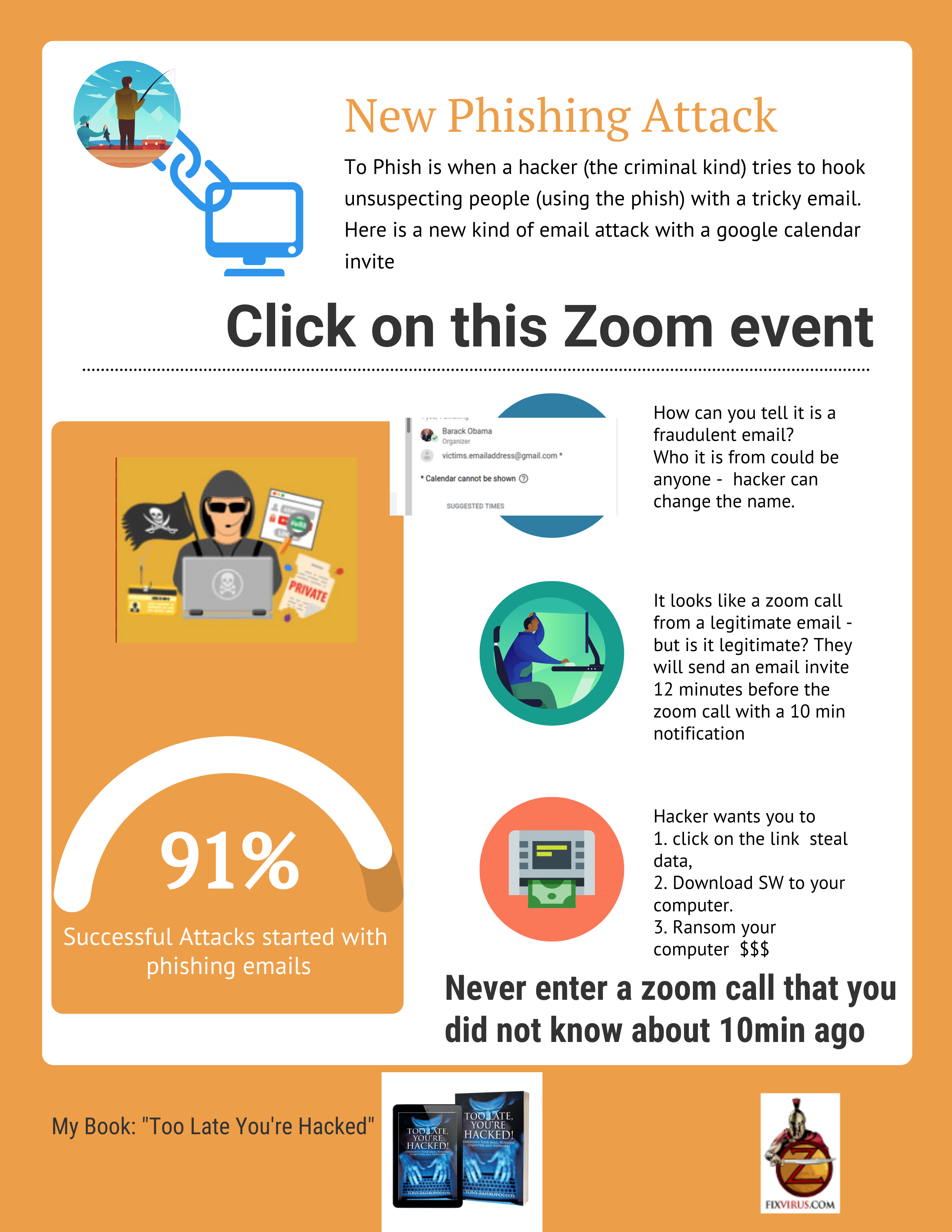
Phishing is successful when it is good enough for a cursory glance… If the user is busy and sees the email and makes sense it works when it is good enough – it does not have to be perfect.
So this new calendar invite set up to get you to click on the link.
Once the link is clicked it can do a variety of things – depends on the criminal hacker and the goals.
Could attempt to install ransomware? Could install other software to steal what you type.
This is the most interesting item in the blog(in my mind):
“In order to make this technique work, we want to send the target the meeting invite roughly 12 minutes before the start time of the meeting. We do not want to send a notification email for our malicious meeting, because this will include our gmail address. Thus, we will simply place the ’emergency’ meeting on the victims calendar 12 minutes before the start time, and allow the default ’10 minute reminder’ to notify them that they are about to miss an important meeting.”
So build into the meeting notice a notification with a 10 min reminder, and thus it is another way to create a sense of urgency – which makes people think less and just act.
To be effective the phishing has to be good enough for a small glance and then the criminal is on your machine. Now you are depending on the criminal ability to write software or buy it from another criminal.
Must have a phishing awareness campaign.
contact us or buy my book: