
 | ||
 |  | Whereas Tonis Zafiropoulos, E.I.T., dutifully and meritoriously performed in the position of Co-Chairman, MSPE Information Technology Task Force. Wheras: you have gone the EXTRA MILE for the Missouri Society of Professional Engineers in your endeavors, and its members are exceedingly grateful and wish to recognize the achievements you have made on their behalf. This award was given because we(other co-chair was Bob Becnel) talked the MSPE organization into grabbing the MSPE.org domain name back in the mid nineties (1996 or so). As you can see MSPE.org is Missouri not MN, or MD, or MS. |

| Saint Louis Metropolitan area Phone: 314-504-3974 Tony Zafiropoulos - tonyz"at"fixvirus.com | |

| ||
 | Book on Innovating with IT - Tony Zafiropoulos 01/13/2013 - Have outline and a couple of thousand words. --- TonyZ Resume
LinkedIn profile --- Twitter Feed Fixvirus |
Here are all the posts from 2011 and 2012:
Be careful what you wish for: Microsoft is Cloud Expanding their product line. Including Windows Azure
Also Windows Azure Virtual machines are in the mix. It looks like Microsoft is trying to be accomodating for Linux instances.
what I did not see is an emphasis on security. And we all know Microsoft is more interested in functionality rather than security.
So buyer beware
9/5/12
What if it is a cloud based service - SaaS (Software as a Service)
How to audit software?
Use tools when possible to check password tables. the username and password combination is typically the first line of defense.
If there are online database queries then there must be checks on the SQL database as well. Protecting against SQL-injection attacks is important.
Each company situation is different as they have different configurations.
Acceptable risk levels are also important to consider.
9/4/12
Thus, some of the key factors for management when choosing the IaaS provider are flexible performance (including scalability) and availability while achieving physical and virtual security needs. Breaking down IaaS:
So there can be tax advantages to not owning your own computer infrastructure. since now there is no morecapital expenditure only service.
The IT challenges are different for IaaS.
08/30/12
Let's define a few terms:
First: a Cloud is an application that sits on someone elses computer infrastructure. So to make sure it is secure, one needs to know the security policies in place on the vendor with the infrastructure.
Second: your application must have security policies in place, with password restrictions on the administrator account, including changing the password periodically (every 90days)
Third: check the application for SQL server and script bugs which would allow unauthorized access into the system. This is a tricky analysis, as what is the correct level of security on an application? A good analyzer needs to evaluate this process and ensure that no untoward actions happen on the system.
I will revisit this as time permits...
8/24/12
When reviewing your company security procedures, the password policy is the most important aspect. As this article by arstechnica says:
Specifically... { "The danger of weak password habits is becoming increasingly well-recognized," said Brooks, who at the time blogged about the warnings as the Program Associate for the Center for Democracy and Technology. The warnings, he told me, "show [that] these companies understand how a security breach outside their systems can create a vulnerability within their networks."
The average Web user maintains 25 separate accounts but uses just 6.5 passwords to protect them, according to a landmark study (PDF) from 2007. As the Gawker breach demonstrated, such password reuse, combined with the frequent use of e-mail addresses as user names, means that once hackers have plucked login credentials from one site, they often have the means to compromise dozens of other accounts, too.}
All of us have many usernames and passwords to keep track of:
08/23/12 Use an encrypted password program - learn how to use it to keep your passwords safe... like KeePass
What is six sigma?
A Black Belt is someone who teaches six sigma. Sigma is a statistical term that explains what the variation from the average is like. Essentially 2 Sigma is 95.4 within the average (mean). 6 sigma is 99.9999 within the average. So the idea is to have as few defects (or variations) as possible to reduce the problems in a process.
Here is an interesting tidbit from the website: {According to the Six Sigma Academy, Black Belts save companies approximately $230,000 per project and can complete four to 6 projects per year}.
That is the reason six sigma is important and saves money.
08/14/2012
itsecurity.comhas a list of audit tasks:
08/10/12
Kaspersky is a good program, but it is too intrusive in my opinion.
I am currently installing Microsoft Security Essentials (free) Download it here on many computers I manage.
In case you bumped into my website looking for anti-virus advice ;)...
Here is the PCMag.com review of anti-virus software. And most interesting is that the Mac platform now has anti-virus software. PCMag likes Norton Anti-virus 2012.
One thing that I would definitely do if you are going to buy anti-virus software, make sure you are updating the whole software engine and not just paying year after year for definition file updates.
06/21/2012
This picture shows the different philosophies of where to place the IPS device:

This is a Corero image - and on the left the Corero method of installing an IPS (before the firewall).
10/12/2011
Corero IPS solution has an interesting take on where the IPS should be placed.
Corero believes their IPS should be placed outside of the firewall, inbetween the firewall and the ISP router.
Many other professionals I have talked to believe this will create too high of a vulnerability, I guess we believe in the firewall acting as perimeter defense.
10/11/2011
Checkpoint has an IPS/firewall unit
The UTM-1 Edge N Series has 6 ports and 1Gbps throughput at about $700, it seems to be decent system for a small business with a small budget.
10/10/2011
Microsoft Security Advance Bulletin Link
3 business days before patch Tuesday (2nd Tuesday of the month) the advance bulletin explains what will be updated (on 10/11/11)
From Microsoft links:
Bulletin ID-- Maximum Severity Rating and Vulnerability Impact ------------------------- Affected Software
Always good to know what is coming in a few days. These patches must be applied to prevent vulnerabilities in the code being taken advantage of.
10/06/2011
In choosing an Intrusion Prevention System keep the following 7 things in mind:
1) Placing the IPS in the right place is very important - (behind a firewall) it has to have a significant chunk of traffic so as to inspect and protect your network.
2) Set up or configure the IPS with the proper tuning parameters which is dependent on your network configuration (protecting web server farm for example)
3) Remember to keep in mind the availability of your network, as the IPS can have problems as well (IBM's IPS had bypass units), in case of a reboot or other issue what should the network availability be?
4) Create a way to test new blocking parameters before using on the production network environment
5) Training and testing on the IPS is a useful and even mandatory in todays network needs
6) Frequent upgrades require testing on a test environment - may be expensive but necessary as the systems need proper vetting before trying new tags and blocking tests.
7) Process improvements are necessary - keep improving the train, test, and production implementation.
10/05/2011
TippingPoint is HP's line for Intrusion Prevention systems
The N platform bundles have 10Gbps throughput capabilities.
HP has not mentioned that it would get out of this business (unlike their PC line).
The technical datasheet for HP TippingPoint.
10/04/2011
I used snort almost right after it was put together (1998 by Martin Roesch) around 2000 I downloaded it and ran a honeypot on my network.
10/01/2011
A little snippet from McAfee datasheet:
Protect your systems
� Proactive protection for unpatched systems
� Proactive protection for zero-day attacks
� System-aware intrusion prevention system (IPS) with McAfee ePO integration
� Host IPS/virus/spyware event visibility
09/28/2011
Juniper Product IDP800  ,
,
I am including this since it is the comparison with the GX5 series from IBM: IDP800 specs.
with a 1Gbps throughput.
09/26/2011
About the different IPS systems from 6 different vendors: Cisco, McAfee, Juniper, IBM, Sourcefire and TippingPoint.
This is definitely an interesting sentence: "These same six providers also rank highest in terms of their effectiveness on the latest Gartner report, although CIsco and IBM are considered to be challengers to the market led by the other four vendors."
So it definitely should be read as a good overview.
09/25/2011
cisco IPS solutions
the National institute of Standards and technology have a paper on IPS systems: NIST paper
09/24/2011

Notice that the lower Green cables on the bypass (the application ports) connect to the IPS.
the upper cables are the network side and connect to the two devices that the IPS will inspect traffic.
The reason the bypass device is there to ensure uptime for the network inspection link. Just in case the IPS device GX5008 has a serious problem, there is a physical 'bypass', and will of course not inspect any traffic, but there is no downtime for your network link.
When rebooting the GX5008, there will be momentary loss of network as the bypass takes over, but the network will come back in seconds.
Although some of the newer units like the GX6116(16 interfaces or 8 links) has a built-in bypass. Also has 5Gbps processing ability.
For comparison the GX5008 has 1Gbps, and the GX4004 has 200Mbps throughput.
9/18/2011
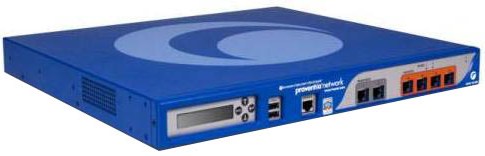
Here is a wholesaler who sells GX4004 Proventia systems Proventiaworks.
The system is actually one of the smaller systems, and only has copper interfaces. So if you need fiber, you have to go with the GX5000 series systems, and they come in many different flavors.
Also worked with the GX5008, GX5108, and GX5208 systems.
9/14/2011
The organization's history link.
formerly the Information Systems Audit and Control Association.
there was an interesting Oracle presentation at the SecureWorldExpo at Americas center - downtown Saint Louis.
9/12/2011
Since SMS messages do not get backed up consider getting: SMS Backup application backups your SMS messges to your Google account.
Also another app if you want to transfer your current SMS messages to another phone (in case of an upgrade or a replacement) SMS Backup and Restore
09/05/2011

Managing Proventia Network Intrusion Prevention Systems (NIPS) by ISS - Internet Security Systems. Actually IBM has purchased ISS, so these are IBM devices now.
Essentially these are inline network devices. they inspect all network traffic in layer 2.
Running Linux CentOS, with proprietary systems for the inline network inspection software system.
Here is a reseller with the GX5108, which can inspect more than 1GB/s ProventiaWorks.com
Tony Zafiropoulos
1/29/11
